FAQ
-
Hardware connection (video)
-
What Is a Location?
Location is a place, where the monitoring system is installed. For example, it could be a store, a warehouse or a building. The system supports an infinite number of Locations for each user.
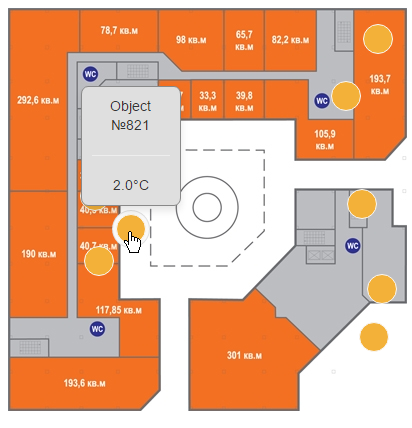
The user can upload any image (a plan) for the Location, and place the equipment on this plan arbitrarily. This makes it possible to keep the status of various control areas (Objects) with the help of the information displayed.
Using the monitoring system, you can review all of yours Locations and share them with other users.
Example of the Location plan with the Objects placement:
-
What Is a Collector?
Collector is a device that provides the information capture from a quantity of sensors and transmitting this data to the server.
Each collector supports 250 sensors and provides the information capture spanning 50-70 meters.
If it is necessary , the operating range may be extended by one or more signal re-translators. Using the re-translators, the range of data capture can be 500-600 meters.

-
What Is an Object?
The object is a zone of the control, consisting of one or more sensors measuring physical parameters.
For example, an object could be a refrigerator or cupboard, equipped with wireless sensors.
The User can upload an image (a photo) of each Object and place sensors on this image arbitrarily. This allows to control parameters visually and search for needed sensor quickly.
Example of the Object plan with the sensors placement:

-
What Is a Sensor?
Sensor is a wireless device that provides a physical value measurement and transmission of data to the Collector.
There are different versions of sensors for measuring different physical values.
-
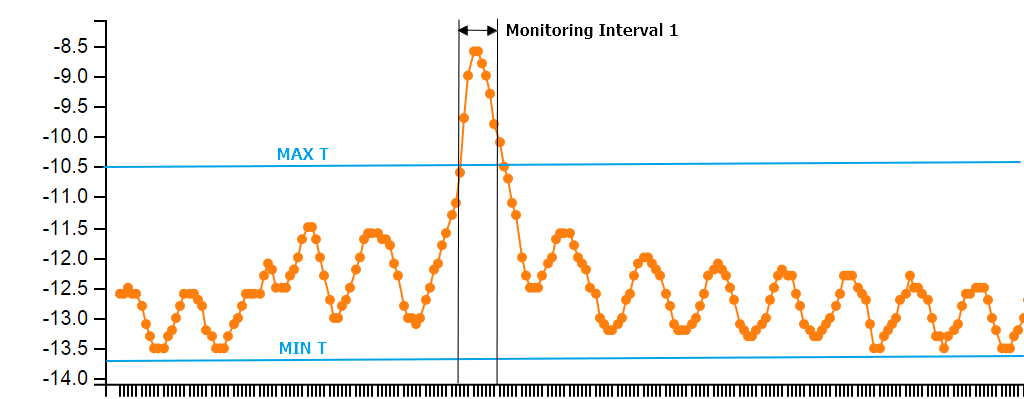
What Is a Monitoring Interval?
Any physical value such as temperature, varies eventually. The system can be configured so that the user will receive a notice each time when the measured value has exceeded the set range.
Practically, a short-term bounds violation must often be filtered out.
For example, any refrigerator automatically switches defrost during which period the camera's internal temperature rises.
Monitoring Interval is used for the Monitoring System to determine a similar operation automatically and to send notifications only when there is need.
Example 1:
The temperature is outside of range and didn't turn back.
In this case, the notification will be sent.
Example 2:
The temperature is outside of range and turned back within the Monitoring Interval.
In this case, the notification won't be sent.
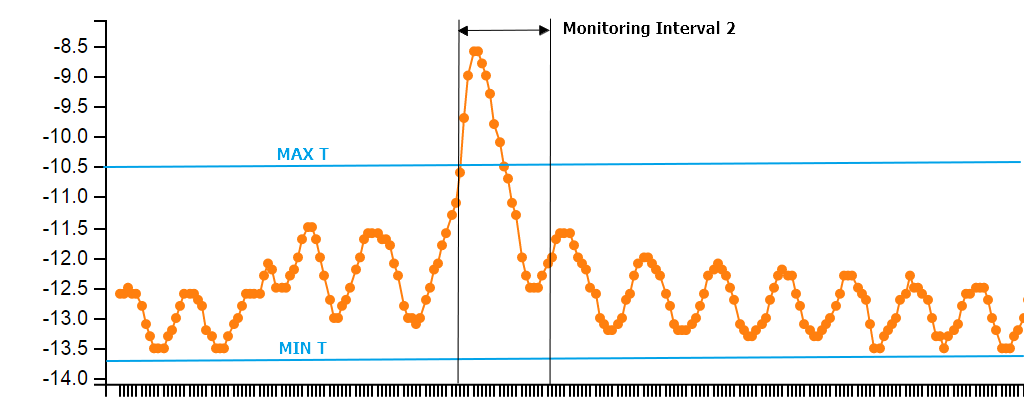
The System provides an opportunity to configure the Monitoring Interval for each Sensor.
-
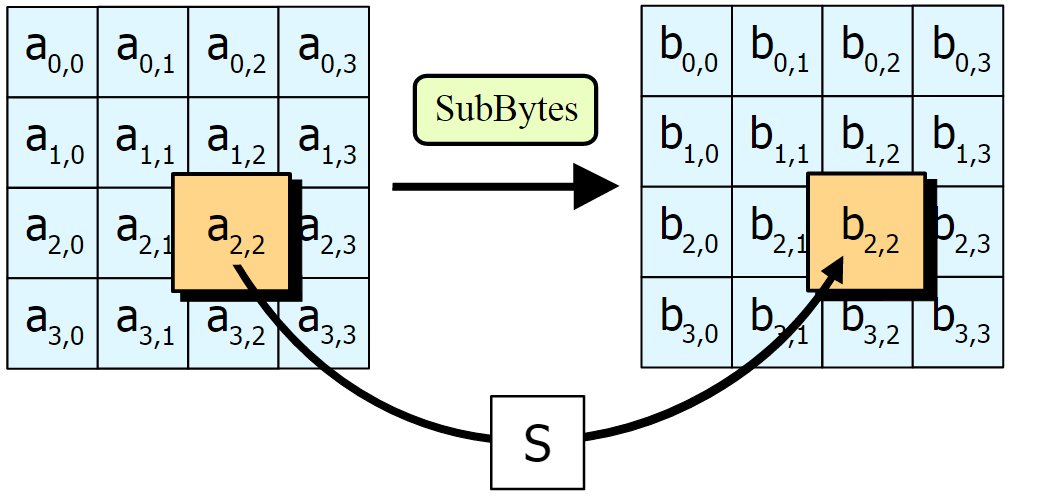
How safe is the data, transmitted by the System of Monitoring?
The Monitoring System uses AES128 for all messages, transmitted by radio and on the server. Each message, sent by an any component of the Monitoring System contains a unique code that changes with each new message. Consequently, an intruder won`t be able to overhear the traffic and sabotage the system by an analogical message.
In June 2003 the U.S. National Security Agency announced that AES could be used to protect classified information.
-
What levels of information access does the System provide?
There are three types of users in the system: the Administrator, the Moderator and the User.
The opportunities for each type of user are listed below.
The Administrator
1. can connect new devices to the system
2. can change any settings
3. can create the administrators, the moderators and the users
4. can remove the administrators, moderators and users
5. can control the access to different Locations and Objects
The Moderator
1. can connect new devices to the system
2. can change any settings
3. can create the moderators and the users
4. can remove moderators and users
5. can control the access to different Locations and Objects
The User
1. can scan allowed Locations and Objects
2. can change settings of that user only, but not to the whole System . -
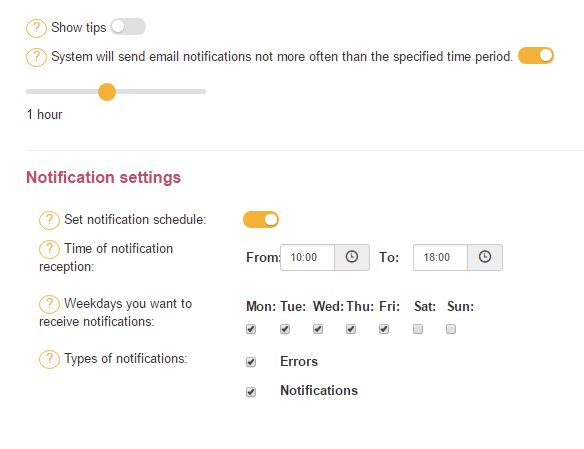
How to setup E-mail notification?
The monitoring system gives various possibilities for e-mail notification setting. Users can set notification time and schedule, as also choose the type of notifications.
There are two types of notifications:
NOTIFICATIONS
System sending user the information about system work and about some failures.
Example: temperature has exceeded setting value.
ERRORS
System is sending user the information about system failures.
Example: low battery in the sensor 123456789.
Notification schedule can be set on the PROFILE tab.
-
How can I instruct the system to create right notifications?
The system creates notifications in cases when measured by sensor values are out of the set value.
The user can set limit values to each of the Objects, and for every sensor individually.
To set limit value, go to SETTINGS, and click necessary Object or sensor in the list. Afterwards click the button SENSOR SETTING and fill in necessary values:
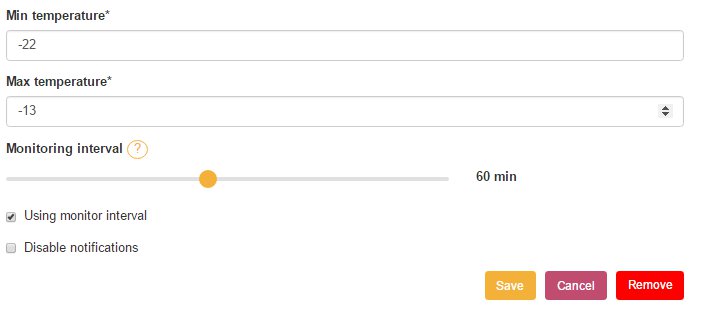
Note: only the user with ADMINISTATOR rights can change values of the objects and sensors.